Secure Telemetry Contracts for Device + AI Stacks

Telemetry is supposed to be your safest window into production reality. But in device + AI systems, it’s also the quickest way to leak sensitive context—quietly, accidentally, and at scale.
The pattern is familiar: a “temporary” debug field ships, raw sensor payloads sneak into logs, verbose metadata encodes identity or location, or a rare failure path dumps buffers that were never meant to leave the device. Once that data enters your ingestion pipeline, it tends to replicate—into log stores, analytics, traces, model-training buckets, and alert snapshots. You don’t get one mistake; you get a distribution channel.
This post shows a contract-first approach: a Secure Telemetry Contract enforced across firmware → edge host (Linux/CM4-class) → cloud ingestion. Firmware emits only typed, bounded, allow-listed events. The host acts as a schema firewall and deterministic redactor. The backend accepts only contract-compliant payloads and enforces invariants like “never upload raw”—even if a device misbehaves. The goal is privacy-safe observability without losing the ability to debug capture pipelines, bus streaming health, AI quality, and fleet reliability.
The core problem: telemetry becomes a covert data plane
In a device + AI stack, telemetry sits adjacent to everything sensitive:
- Sensor buffers (RGB, thermal, audio, IMU)
- Environment identifiers (Wi-Fi SSIDs, BLE addresses, GPS hints)
- User context (names, pet names, household schedule patterns)
- Model inputs/outputs (embeddings, prompts, intermediate features)
- “Helpful” traces (full request/response bodies)
The leak modes are rarely malicious. They’re operational:
- Debug dumps become production behavior
A one-line “log the buffer if parsing fails” becomes a permanent rare-path leak. - Metadata expands over time
Teams add fields to improve diagnosis (“just add SSID, it helps”), and those fields persist forever. - Raw payloads hitchhike through generic pipelines
A blob field slips into a JSON envelope, then gets mirrored to multiple stores. - Cloud logging/tracing captures everything by default
Frameworks record request bodies, headers, and stack traces—sometimes including secrets.
The result: “observability” becomes a covert exfiltration channel.
Approach: Treat telemetry as a product interface, not a log stream
A Secure Telemetry Contract is a versioned, enforceable interface with these properties:
- Allow-list schemas: only known event types and fields exist
- Hard bounds: size limits, enumerations, range constraints, truncation rules
- Deterministic redaction: same input → same safe output, no heuristics
- Debug-gated raw paths: rare, time-bounded, explicitly authorized, and auditable
- Backend invariants: “accept only contract-compliant payloads” + “never upload raw”
- Testability: you can prove certain data cannot reach production sinks
This is not “be careful with logs.” It’s architecture that makes unsafe behavior hard or impossible.
The contract: a strict telemetry envelope
Start by standardizing a single envelope that every event must use. Keep it boring, typed, and bounded.
Envelope (example):
contract_version(semver or monotonic int)device_id(opaque, non-PII, rotated identifier; no MAC)fw_version,host_versionevent_type(enum)ts_ms(monotonic + wall clock rules)severity(enum: debug/info/warn/error)payload(typed object constrained by event schema)signatures/integrity(CRC/HMAC as appropriate)debug_context(optional, only when debug gate is active)
Design rules that matter:
- No free-form strings unless strictly bounded and justified
- No “metadata” map or untyped “attributes”
- No base64 blobs in production events
- No raw sensor payload fields in the contract at all
Bounded fields: the underrated security feature
Bounds aren’t just performance guards—they’re privacy guards.
Examples:
ssid_hash: fixed-length hex string, not SSIDerror_message: max 120 chars; device-side normalization (no buffer printing)stack_hash: hash of a symbolized stack trace, not the trace itselfimage_stats: numeric summaries (histograms, ROI size), not pixels

Layer 1: firmware emits only typed, bounded events
Firmware is where you win or lose. If raw content ever enters the telemetry stream here, downstream controls become cleanup, not prevention.
Firmware rules
- Event types are enums, not strings
- Payloads are structs with fixed fields
- All strings are bounded and sanitized
- No raw buffers in telemetry
- No dynamic “extra fields”
- Explicit byte-budget per event type
Example: “capture pipeline health” event
Instead of: “log the failed frame bytes”
Emit: “what happened, where, and how often”
Payload ideas:
- capture state enum:
STARTED | FRAME_DROPPED | ROI_EXTRACTED | COMMITTED - counters: dropped frames, CRC failures
- timing:
capture_ms,queue_depth - summary stats: mean thermal value in ROI, not full thermal map
Implementation note: contract compilation
A practical trick: define schemas once (IDL/JSON schema/protobuf) and generate:
- firmware struct definitions
- host validators
- backend parsers
This reduces drift and “manual interpretation” bugs.
Layer 2: Edge host as schema firewall + deterministic redactor
The edge host is your enforcement point with more compute and update agility than firmware. Treat it like a border router for data.
What the host must do
- Verify envelope integrity (CRC/HMAC, monotonic counters)
- Validate schema (event_type must match known version)
- Reject unknown fields (fail closed)
- Apply deterministic redaction (consistent transformations)
- Enforce budgets (per-device/per-minute/per-event caps)
- Route only contract-compliant events to cloud
“Schema firewall” = fail closed, not best effort
If an event contains unknown fields, don’t strip them and forward. Reject and emit a local-only diagnostic counter:
telemetry_rejected_unknown_field_counttelemetry_rejected_oversize_count
This prevents a compromised or buggy device from “discovering” what the cloud accepts.
Deterministic redaction patterns that work
- Hashing with rotation (e.g., SSID → salted hash, salt rotates)
- Bucketization (RSSI values bucketed to ranges)
- Truncation (error strings cut to max length)
- Allow-list normalization (map error codes to a controlled enum)
- Token stripping (remove headers, auth strings, URLs with query params)
Deterministic matters because:
- It’s testable
- It avoids heuristic misses
- It prevents “special cases” that leak

Debug-gated raw paths: how to investigate without turning on a firehose
If you can’t ever see raw data, you’ll eventually reintroduce raw dumps “just for this incident.” So you need a designed, constrained escape hatch.
A good debug-gated raw path is:
- Build-gated: only enabled in specific firmware/host builds (or feature flags with cryptographic authorization)
- Time-bounded: expires automatically (minutes/hours, not days)
- Scoped: per-device, per-sensor, per-module
- Rate-limited: hard caps, fixed budgets
- Explicitly authorized: signed token or certificate-based unlock
- Audited: every enablement generates an immutable record
- Separate sink: never the same pipeline as normal telemetry
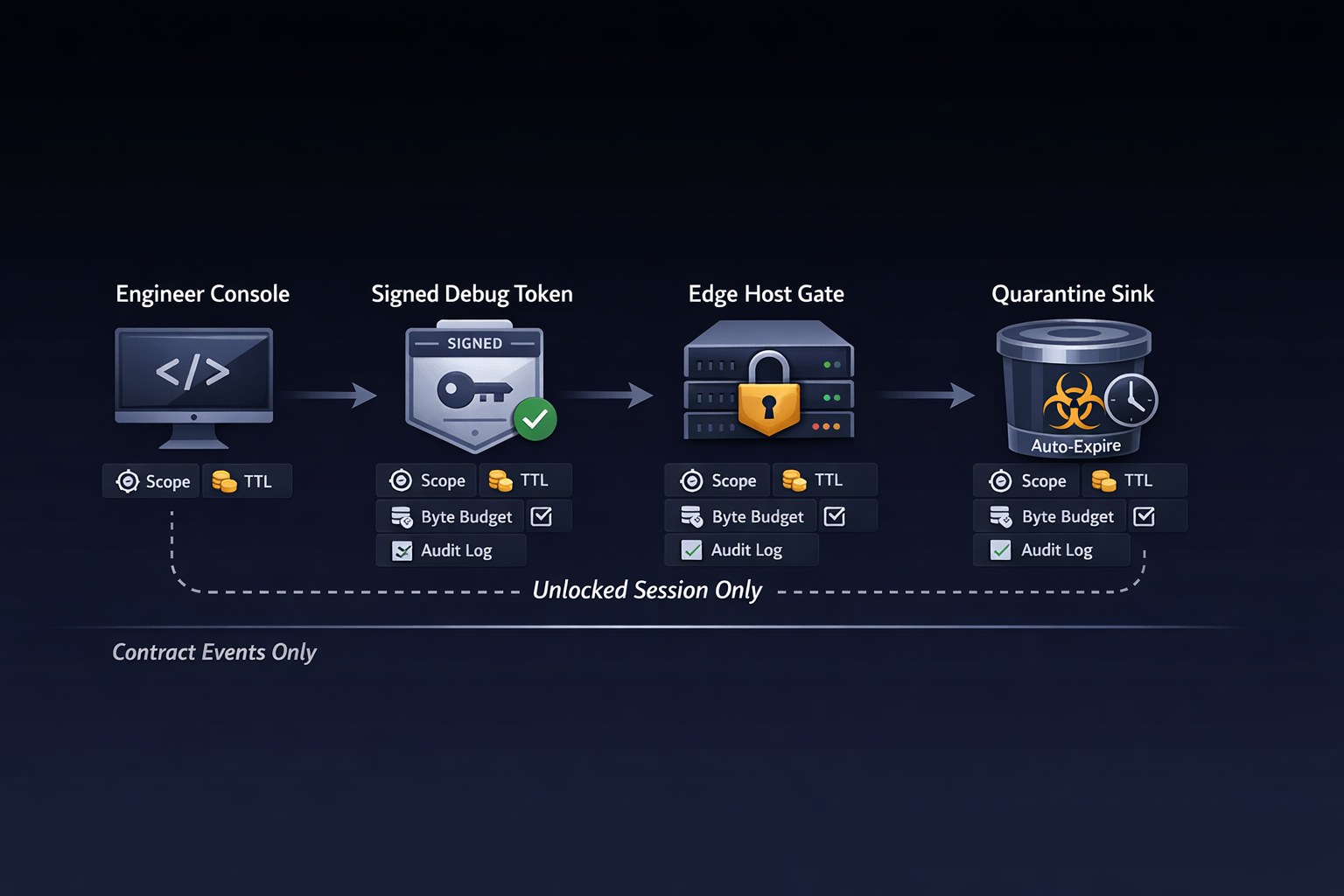
Debug gate mechanism (pattern)
- Engineer requests debug session for
device_id - Backend issues a signed debug token with:
- scope:
camera_roi_dump,thermal_roi_dump, etc. - duration: e.g., 20 minutes
- max bytes: e.g., 5 MB total
- scope:
- Host validates token, flips a local gate
- Raw artifacts go to a quarantine bucket with:
- stricter access controls
- auto-expiration
- no replication into analytics/training by default
Raw path content should still be minimized
Even in debug mode:
- Prefer ROI over full-frame
- Prefer downsampled content
- Prefer short windows
- Prefer on-device preprocessing
Layer 3: backend accepts only contract-compliant telemetry
Cloud ingestion needs to be as strict as the host—otherwise it becomes the “forgiving layer” that attackers and bugs exploit.
Backend invariants (non-negotiable)
- Reject unknown event types or versions
- Reject unknown fields (fail closed)
- Reject oversize payloads
- Reject any raw payload fields (even if present)
- Never store request bodies in logs
- Separate operational telemetry from ML/training data
- Attach provenance: device + host versions, validation outcome
Practical controls
- API Gateway / ALB request size limits
- Strict JSON/protobuf decoding with “unknown field = error”
- WAF rules for payload patterns you never expect
- Structured logging that never prints payload by default
- Sampling policies that do not sample “full event bodies”
AI-specific: stop raw from entering model pipelines
A common failure mode is “telemetry doubles as training data.” Avoid this by design:
- Telemetry contains health + summaries, not raw features
- Training data is a separate, consented, explicitly curated dataset
- Debug artifacts stay quarantined unless manually promoted
Validation: prove sensitive fields can’t reach production
Tests to implement
- Schema fuzzing: random fields, random nesting → must reject
- Oversize tests: payload exceeds bounds → must reject
- Forbidden-field tests:
raw_image,raw_audio,ssid→ must reject - Debug gate tests: raw path when gate off → must reject + alert
- End-to-end property tests: “no raw bytes appear in logs/storage”
Audit checks (continuous)
- “Top unknown-field rejections by firmware version”
- “Any raw sink writes without an active debug session”
- “Events with unusually high entropy strings”
- “Storage scans for forbidden keys/patterns”
Results: what “good” looks like in production
You’ll know the contract is working when:
- Incidents are diagnosable using structured health events:
- capture pipeline state transitions
- CAN/bus health counters
- queue depths and timing percentiles
- model inference health signals (latency buckets, confidence summaries)
- Sensitive context stays off the wire by default
- no raw images/audio in telemetry
- no environment identifiers in logs
- no “temporary” debug fields surviving release trains
- Debug is deliberate, not accidental
- raw access is session-based and expires
- quarantine sinks are controlled and auto-cleaned
- audits show who enabled what and when
If you want to include metrics in your own system, measure things like:
- rejection rate
- unknown-field counts by firmware version
- debug sessions per week and average duration
- bytes written to quarantine vs normal telemetry
- mean time to diagnosis (MTTD) before/after contract enforcement
Hoomanely builds connected pet-health devices and AI-backed experiences. In that kind of ecosystem, the value comes from reliable insights—not from collecting everything. Secure telemetry contracts make it possible to operate devices (including camera/thermal-enabled hardware like EverBowl, and wearable-style telemetry like EverSense) with privacy by construction: diagnosis stays strong while sensitive context stays out of default pipelines.
In practice, this contract-first approach becomes part of the engineering culture:
- firmware changes ship with schema diffs
- host rejects drift immediately (no silent acceptance)
- cloud ingestion stays strict, even under incident pressure
- raw investigations are rare, scoped, and auditable
Key takeaways
- Telemetry is a data plane. Treat it like an API contract, not a log stream.
- Fail closed everywhere. Firmware emits allow-listed events; host and cloud reject unknowns.
- Bounds are privacy controls. Size limits, enums, and truncation rules reduce leak surface.
- Redaction must be deterministic. Heuristics fail silently; deterministic transforms can be proven.
- Debug raw paths should exist—but be gated. Scoped, time-bounded, budgeted, audited, quarantined.
- Prove it with tests and audits. If you can’t demonstrate “raw can’t reach prod,” it eventually will.